Getting started
Create a new VPC
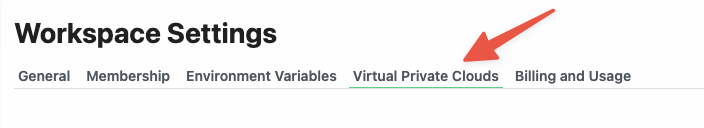
- Open the Virtual Private Clouds tab:
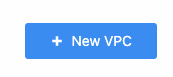
- Click on New VPC in the upper right of the page:
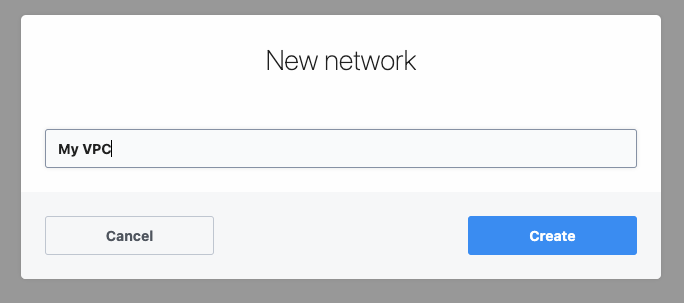
- Enter a network name and click Create:
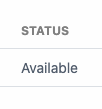
- It may take 5-10 minutes to complete setting up your network. The status will change to Available when complete:
Run workflows within a VPC
To run workflows in a VPC, check the Run in Private Network option in workflow settings and select the network you created. All outbound network requests for the workflow will originate from the static egress IP for the VPC (both when testing a workflow or when running the workflow in production).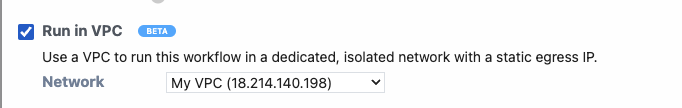
Find the static outbound IP address for a VPC
You can view and copy the static outbound IP address for each VPC in your workspace from the Virtual Private Cloud settings. If you need to restrict access to sensitive resources (e.g., a database) by IP address, copy this address and configure it in your application with the/32 CIDR block. Network requests from workflows running in the VPC will originate from this address.

Managing a VPC
To rename or delete a VPC, navigate to the Virtual Private Cloud settings for your workspace and select the option from the menu to the right of the VPC you want to manage.Self-hosting and VPC peering
If you’re interested in running Pipedream workflows in your own infrastructure, or configure VPC peering to allow Pipedream to communicate to resources in a private network, please reach out to our Sales team.Limitations
- Only workflows can run in VPCs (other resources like sources or data stores are not currently supported). For example, sources cannot yet run in VPCs.
- Creating a new network can take up to 5 minutes. Deploying your first workflow into a new network and testing that workflow for the first time can take up to 1 min. Subsequent operations should be as fast as normal.
- VPCs only provide static IPs for outbound network requests. This feature does not provide a static IP for or otherwise restrict inbound requests.
- You can’t set a default network for all new workflows in a workspace or project (you must select the network every time you create a new workflow). Please reach out if you’re interesting in imposing controls like this in your workspace.
-
Workflows running in a VPC will still route specific requests routed through the shared Pipedream network:
$.send.http()requests- Async options requests (these are requests that are made to populate options in drop down menus for actions while a building a workflow — e.g., the option to “select a Google Sheet” when using the “add row to Google Sheets” action)
FAQ
Will HTTP requests sent from Node.js, Python and the HTTP request steps use the assigned static IP address?
Yes, all steps that send HTTP requests from a workflow assigned to a VPC will use that VPC’s IP address to send HTTP requests. This will also includeaxios, requests, fetch or any HTTP client you prefer in your language of choice.
The only exception are requests sent by $.send.http() or the HTTP requests used to populate async options that power props like “Select a Google Sheet” or “Select a Slack channel”. These requests will route through the standard set of Pipedream IP addresses.